In 2017 61% of small businesses in the United States suffered some kind of cyber-attack according to a report by the Ponemon Institute. This number reflects an over 50% increase year to year in cybersecurity assaults on U.S. small businesses. Even more discerning is that an August, 2020 report from Interpol is that 43% of small to mid-size businesses do not have any cybersecurity plans whatsoever. This includes no endpoint detection, malware detection, firewalls/basic defenses, and incident response/contingency plans.
There are many reasons why small businesses need cybersecurity — privacy, client trust, systems availability, financial data protection, data integrity and the longevity of the business in the face of a changing threat landscape. For a small business owner, the topic of cybersecurity can seem overwhelmingly complex, but a basic understanding of cybersecurity is considered essential for running a business in 2020, particularly a business with any kind of online presence or engagement with its customers. Here are some common sense and helpful cybersecurity controls that any small business should ensure they have employed.
Two-Factor or Multi-Factor Authentication (MFA) should be employed for login systems that support it to increase the security needed for confidential systems. MFA is typically employed on many your cloud providers services such Google Apps, AWS Web Services, Azure/Office 365 that require a second password or code to be used for authentication in addition to your username and password.
Data backups should be enabled on key information systems that support essential business functions. What were to happen in the event of a company laptop or tablet with critical business information breaks or is lost/stolen? Without a data backup service, information on that device would not be recoverable. Companies should look at using a free or paid for data backup cloud service provider. Luckily, many of these services run on devices automatically without user interaction.
Boundary protection is essential for protecting the boundary of your network and infrastructure. Hackers are constantly looking for company devices that are exposed to the internet with open services that are easily exploitable. A router with a combination hardware firewall and IDS system enabled can go a long way to ensure network traffic is properly blocked and filtered entering and leaving your organization.
Endpoint protection are those software service such as Anti-Virus and Malware that run on your laptops, tablets, and phones to ensure nefarious software is not installed and exploited on company assets. Endpoint protection includes services like Microsoft Defender and Symantec Endpoint Protection that are free or small cost that provides ernmous security benefits.
Cybersecurity threats are great and can be overwhelming for a small business. Grove is here to help. With extensive experience in security architecture and engineering services, our Grove consultants can work with you on prioritizing the cybersecurity needs tailored specifically for your business. Schedule a call with one of our consultants today!
AI Usage Transparency Report
Pre-AI Era · Written before widespread use of generative AI tools
AI Signal Composition
Score: 0.01 · Low AI Influence
Summary
Cybersecurity is crucial for small businesses to protect privacy, client trust, systems availability, financial data, and longevity. Employing basic cybersecurity controls such as MFA, data backups, boundary protection, and endpoint protection can help prevent cyber-attacks.
Related Posts
Setting up Ollama on macOS
Recently, after some bad experiences with OpenAI's ChatGPT and CODEX, I decided to look into and learn more about running local AI models. On its face it was intimidating, but I had seen a lot of people in the MacAdmins community posting examples of macOS setups, which really helped lower the bar for me both in terms of approachability and just making me more aware of the local AI community that exists out there today.
AI Agent Constraints and Security
I really feel like in this era of AI it's essential to write about and share experiences for others who are leveraging AI, especially now that AI usage seems almost ubiquitous. Specifically, when it comes to AI in development and the rapid growth of AI-driven automations in the IT landscape, I believe there's a need for open discussion and exploration.
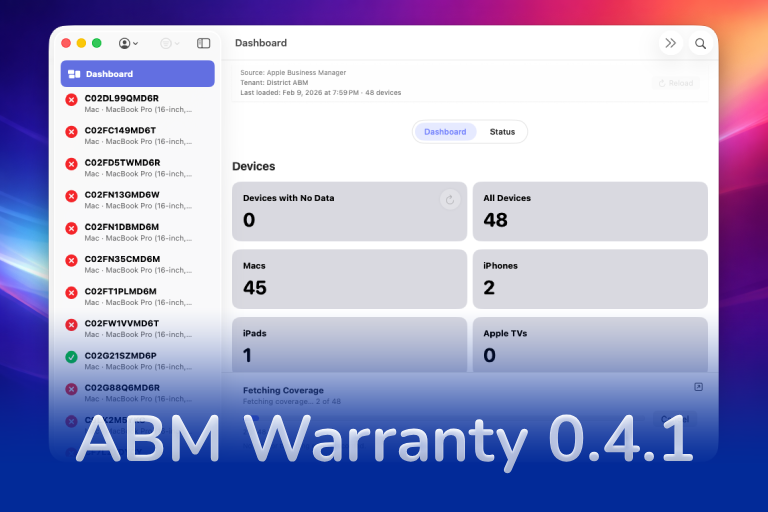
ABM Warranty 0.4.1
The 0.4.x release series for ABM Warranty is focused on operational scale. The earlier 0.3 releases were about trust, correctness, and stabilizing the foundation. Version 0.4.1 builds directly on that work by making the app more practical for consultants, internal IT teams, and managed service providers who need to support multiple environments without losing isolation, control, or visibility. This includes improvements to user interface and workflow, as well as enhanced reporting capabilities to help these users manage their workflows more efficiently.
Vibe Coding with Codex: From Fun to Frustration
So there I was, a typically day, a typical weekend. As a ChatGPT customer, I had heard good things about Codex and had not yet tried the platform. To date my experience with agentic coding was simply snippit based support with ChatGPT and Gemeni where I would ask questions, get explanations and support with squashing bugs in a few apps that I work on, for fun, on the side. There were a few core features in one of the apps I built that I wanted to try implementing but the...
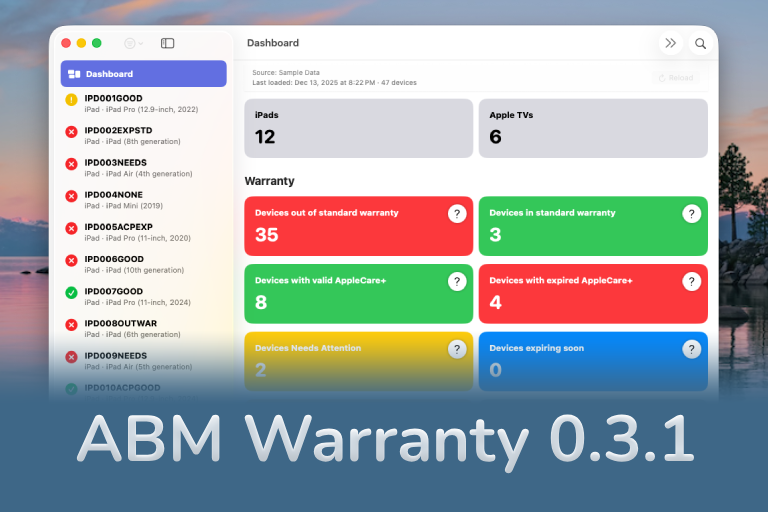
The warranty dashboard Apple doesn’t provide… yet
Download ABM Warranty
Why Apple Fleet Risk Isn’t a Security Problem—Until It Is
Security and risk are often treated as interchangeable concepts in modern IT environments, but they are not the same discipline. Security focuses on controls, enforcement, and prevention. Risk management, by contrast, is concerned with likelihood, impact, and consequence across operational, financial, and organizational domains. Frameworks such as those published by NIST make this distinction explicit: risk assessment is not a technical exercise, but a business one. Technology informs risk decisions, but it does not define them.
ABM Warranty 0.3.1
The 0.3.x release series for ABM Warranty is about tightening guarantees. Where earlier releases focused on surfacing data and making long-running operations observable, 0.3.x focuses on ensuring that what you see is complete, consistent, and safe to trust—particularly as the app is used in larger, slower, and more varied environments. This shift in focus aims to provide a more reliable foundation for users who require higher levels of assurance from their warranty management system.
ABM Warranty 0.2.0
ABM Warranty 0.2.0 is a feature release focused on visibility, safety, and scale. This version does not change what ABM Warranty is meant to be, but it significantly improves how the app behaves under real-world conditions—large device counts, API throttling, long-running imports, and the kinds of failure modes Apple IT admins actually encounter. The improvements in this release are designed to make the app more reliable and efficient, allowing it to handle complex scenarios without breaking or becoming unresponsive.
Running a Beta Program: Lessons Learned
Shipping software in isolation is comforting. You control the inputs, the environment, and the narrative you tell yourself about how things work. The moment you invite other people in—especially people who don’t share your assumptions—you lose that comfort. You also gain something far more valuable. Running a public beta for ABM Warranty through Apple’s TestFlight program forced me to confront that tradeoff head-on, and it fundamentally changed how quickly and confidently the app matured.
The Day I Unmanaged a Mac Into a Corner
There are a few kinds of mistakes you make as a Mac admin. There are the ones that cost you time, the ones that cost you sleep, and then there are the ones that leave you staring at a perfectly good laptop thinking, “How did I possibly make this *less* manageable by touching it?” These mistakes often stem from a lack of understanding or experience with macOS, but they can also be the result of rushing through tasks or not taking the time to properly plan and test.