The COVID-19 crisis has forced many organizations and businesses to work from home. Are you aware of the cybersecurity risks to your business with your employees working remotely?
As we shift to working from home you’re business has to face new challenges. Verifying the legitimacy of a potential phishing email is not as easy as it once was with new techniques being deployed daily.
How are your computers being managed? Is your data safe? Have you talked about cybersecurity with your staff? COVID-19 is not going away any time soon, its going to pose new risks and challenges for all.
This is the second in our Video Blog series on COVID-19 scams. If you need help with your business and or cybersecurity advice call us and we will be happy to help!
Video Blog
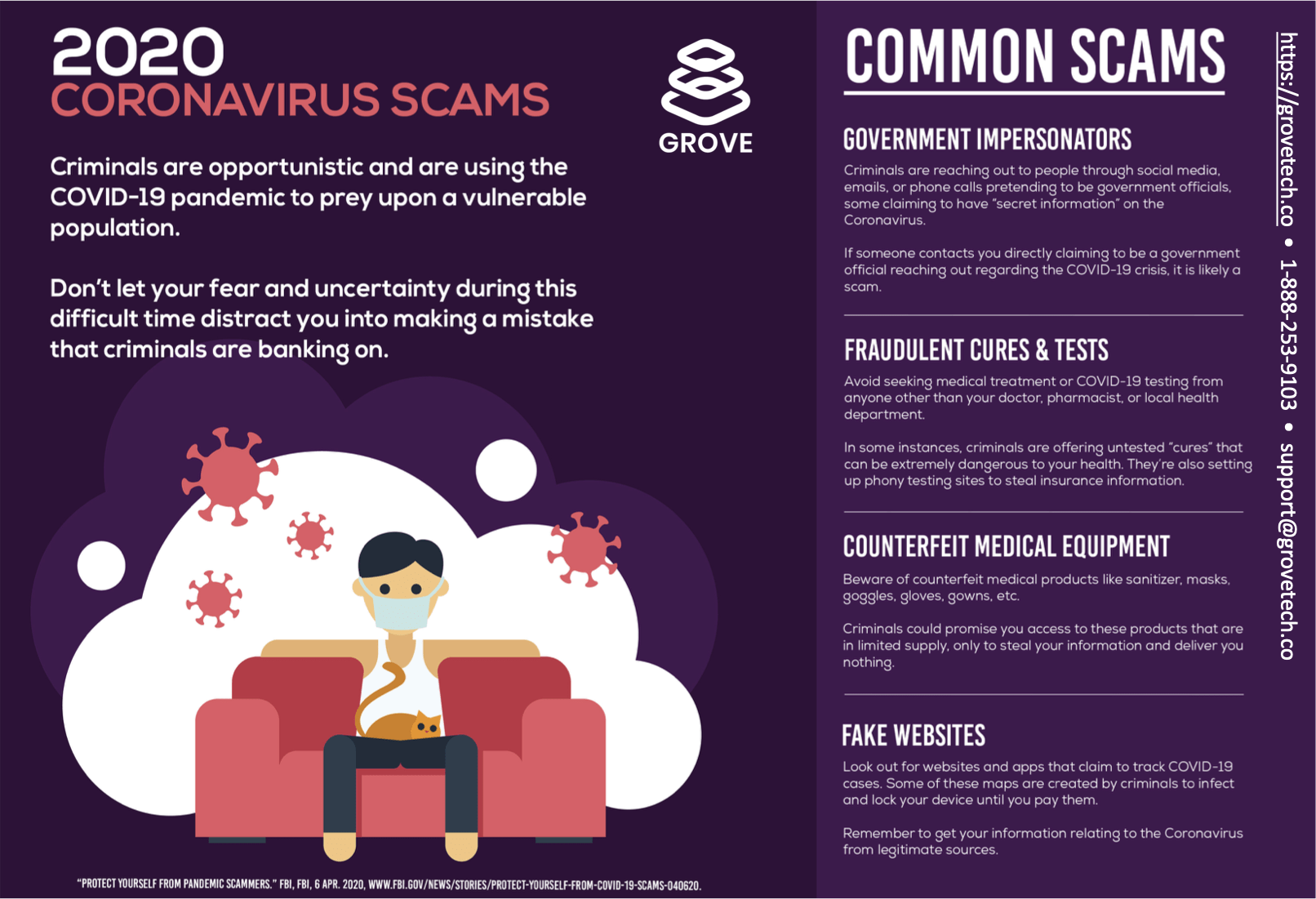
Along with that we have come out with several new guides to keep your team safe and productive. A flyer to distribute to your staff so they are in the know on potential scams and a best practices work from home IT checklist. Both available for free below. We hope you make good use of these resources and reach out if we can be of assistance!
Download the PDF version here.
Download the PDF version here.
If you like our resources please share this page on Facebook, LinkedIn or Twitter with a business that may be struggling or need help. We are offering free 1 hour complimentary checkups for cybersecurity posture to any company that needs a little free advice in these difficult times.
Also please subscribe and follow for more videos, guides, tips and tricks!
AI Usage Transparency Report
Pre-AI Era · Written before widespread use of generative AI tools
AI Signal Composition
Score: 0.04 · Low AI Influence
Summary
The COVID-19 crisis has forced many organizations and businesses to work from home, increasing cybersecurity risks.
Related Posts
Download our White Paper - Penetration Testing for your Business
Organizations are faced with the increasing scrutiny of more complex and sophisticated attacks by threat actors against key information systems that are essential to the organization. Complex attacks such as ransomware and data exfiltration are being used against organizations or systems that they encounter or somehow get access to. When an attacker wants to break into a system, they will typically choose the easiest and most direct methods in means in order to access it. The problem is an organization may not have a full understanding of the complex attack...
Download our White Paper - Why your Small Business needs a vCISO
Cybersecurity risks and threats are issues that all organizations, large and small, must deal with. Whether the issues are information security program related or a technical challenge, organizations need to have the personnel resources to solve the cybersecurity issues as aligned to the business requirements set forth. In an ever-growing cloud-based services industry, information security risk is never greater. Cyberattacks are growing in impact and frequency. Not a week passes without a headline of another cybersecurity attack such as a data breach or a ransomware attack. Cyber criminals are becoming...
Download our White Paper - Cybersecurity Training 101 For Small Businesses
Security awareness training is one of the most critical and important security requirements for any size organization to consider implementing within their environment. Arguably, the greatest risk faced by any organization is the danger of insider threat as employees are can be considered a weak link in the chain as they are susceptible to curiosity, greed, envy, etc. To further increase risk, employees may be faced with the threat of social engineering attacks including phishing, baiting, spear phishing, tailgating, scareware, pretexting, quid pro quo, etc. To combat these risks, a...
Download our White Paper - Cybersecurity Risk Assessments For Small Businesses
A cyber security risk assessment is a critical activity performed on your company's security policy, procedures, and infrastructure to reveal potential threats to key corporate assets and vulnerabilities in your current security controls as implemented. This process involves identifying and evaluating the likelihood and potential impact of these risks, allowing you to prioritize mitigation efforts and allocate resources effectively.
Download our CMMC White Paper and learn what CMMC means for your small business.
The Cybersecurity Maturity Model Certification (CMMC) is the Department of Defense’s (DoD) latest cybersecurity program designed to ensure that cybersecurity controls and processes adequately protect Controlled Unclassified Information (CUI) that resides on Defense Industrial Base (DIB) systems and networks. The DIB consists of all suppliers of DOD related services including primes, subcontractors, consultants, and other entities that provide any type of service on a DOD related contract. This includes companies that manufacture, design, or test products for the DoD, as well as those that provide services such as logistics, maintenance,...
Guidelines for OCR enforcement discretion for telehealth remote communications
The Health Resources and Services Administration (HRSA) of the U.S. Department of Health and Human Services (HHS) defines telehealth as: The use of electronic communication and information technologies, such as video conferencing, phone calls, and messaging systems, to provide healthcare services remotely. This includes consultations, diagnoses, treatments, and patient education.
31 Cybersecurity Awareness Tips for 2020
The internet has gone from strength to strength and part of the beauty of it is the fact that it enables us all to communicate freely with people everywhere in the world. Now with the growth of Wi-Fi we have allowed ourselves to create devices which also connect to the internet and deliver or transfer data within a network. While this connectivity is amazing, the unfortunate downside is that each internet connected individual on the planet has their own networks and their own data that can fall victim to theft...
Remote Work Guide Do's and Dont's
Working remote has many benefits but also creates many cybersecurity risks. Here is a handy list of do's and Dont's to help you protect your company and sensitive information.
Top Tips on Working From Home Securely
The necessity of working from home is becoming a reality for many workforce members who may not have had this access before. While remote working offers many benefits to employees, such as increased flexibility and work-life balance, many more risks appear as cybercriminals prey on the lax security protocols of the remote worker. It is critical that we as employees treat this access as a privilege, making security our top concern in order to protect ourselves and our organizations from potential threats.
COVID19 Protect Your Small Business Data
The threat of the Novel Coronavirus has recently been a top concern worldwide. With many conspiracy theories, disinformation, and general curiosity, many citizens are looking for more information on the outbreak from a trusted source. As a result, it's essential to rely on credible sources when seeking updates or guidance on this issue.