Troubleshooting Standard Routing Policies in JAMF Security Cloud
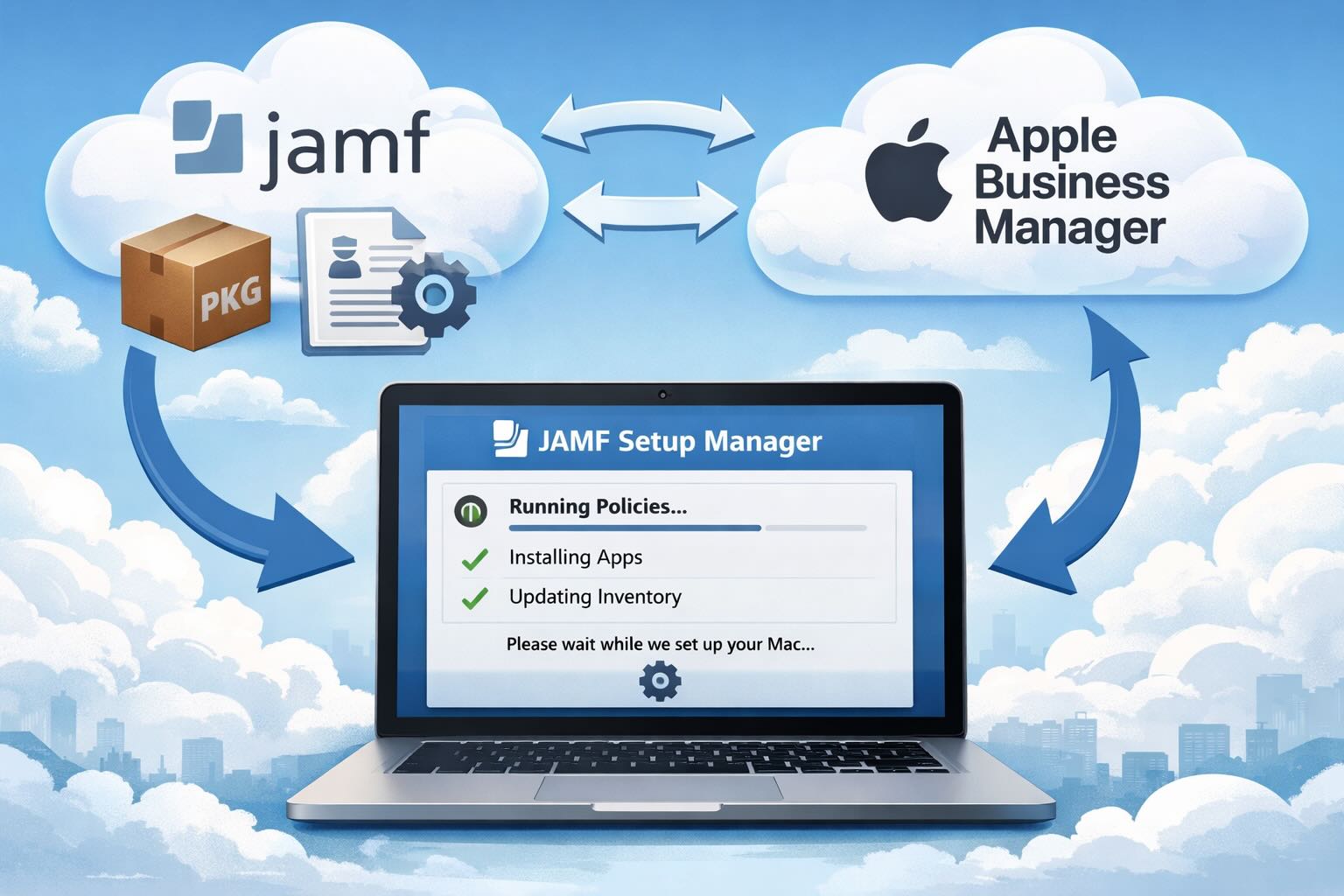
As a fairly new administrator of JAMF Security Cloud, it was the ease of which its administration that admittedly drew me in. Quite an elegant solution for securing the various apps on business workstations with premade app-based VPN routing rules built right in, I was hooked. The concept is simple: turn on the policies, create your enrollment, and deploy – and you're done. This straightforward approach has made it easy to integrate into our existing workflow, allowing us to focus on more critical tasks.